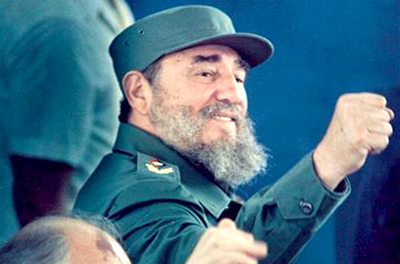
Cuban revolutionary Fidel Castro passed away on Saturday. Here is a look at his life and work in Cuba.
 BIRTH DATE: Officially listed as Aug. 13, 1926, in Cuba's Oriente province, although some say Castro was born a year later.
BIRTH DATE: Officially listed as Aug. 13, 1926, in Cuba's Oriente province, although some say Castro was born a year later.
TITLES: Former president of Council of State and Council of Ministers, first secretary of Communist Party of Cuba, commander in chief of Cuba's Revolutionary Armed Forces. Before resigning Feb. 19, 2008, he was the world's longest-ruling head of government, and leader of one of world's last five communist states. Had been off public stage for year and half after provisionally ceding power to his brother Raul following emergency intestinal surgery.
EDUCATION: Attended Roman Catholic schools and University of Havana, where he earned law and social science degrees.
FAMILY: Married Mirta Diaz-Balart in 1948; son, Fidel Felix Castro Diaz-Balart, born in 1949; divorced in 1955. Although Castro never confirmed remarrying, reportedly wed former schoolteacher Dalia Soto del Valle and had five sons. Also reportedly had several other children out of wedlock.
QUOTE: “Homeland or death! Socialism or death! We shall overcome!”
July 26, 1953: Launched his revolutionary fight by attacking military barracks in eastern city of Santiago. Was arrested, later freed under amnesty deal. Travelled to Mexico to form a rebel army, and returned to Cuba with followers aboard small yacht. Most were killed or captured, but Castro and a small group escaped into eastern mountain strongholds
Jan. 1, 1959 Castro's rebels take power as dictator Fulgencio Batista flees Cuba.
June 1960 Cuba nationalises U.S.-owned oil refineries after they refuse to process Soviet oil. Nearly all other U.S. businesses expropriated by October.
October 1960 Washington bans exports to Cuba, other than food and medicine.
April 16, 1961 Castro declares Cuba socialist state.
April 17, 1961 Bay of Pigs: CIA-backed Cuban exiles stage failed invasion.
Feb, 7, 1962 Washington bans all Cuban imports.
October 1962 U.S. blockade forces removal of Soviet nuclear missiles from Cuba. U.S. President John F. Kennedy agrees privately not to invade Cuba.
March 1968 Castro's government takes over almost all private businesses.
April 1980 Mariel boatlift: Cuba says anyone can leave; some 125,000 Cubans flee.
December 1991 Collapse of Soviet Union devastates Cuban economy.
August 1994 Castro declares he will not stop Cubans trying to leave; some 40,000 take to sea heading for United States.
March 18, 2003 75 Cuban dissidents sentenced to prison.
July 31, 2006 Castro announces has had operation, temporarily cedes power to brother Raul.
Feb. 19, 2008 Castro resigns as president.
July 2010 Castro re-emerges after years in seclusion, visiting a scientific institute, giving a TV interview, talking to academics and even taking in a dolphin show at the aquarium.
April 19, 2011 Castro is replaced by his brother Raul as first secretary of the Communist Party, the last official post he held. The elder Castro made a brief appearance at the Congress, looking frail as a young aide guided him to his seat.
April 19, 2016 Castro delivers a valedictory speech at the Communist Party's seventh Congress, declaring that “soon I'll be like all the others. The time will come for all of us, but the ideas of the Cuban Communists will remain.”
November 25, 2016 Fidel Castro dies





Comments
Add new comment