New York, Feb 1: Search engine giant Google has paid Sanmay Ved, the man who owned Google.com for a minute, $6,006.13 (about Rs 4.07 lakh) and later doubled the amount when he donated his reward to charity.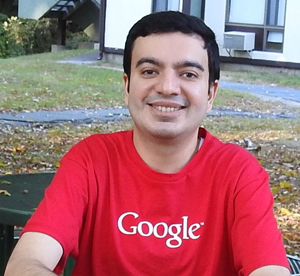
In September last year, the ex-Googler, while searching Google Domains, found that Google.com (domain name) was available for purchase. He bought the domain for $12 and gained access to its webmaster tools before Google cancelled the sale.
However, the Mandvi resident (in country's Kutch region) had said it was never about money and wanted the amount to be donated to the Art of Living India Foundation.
"You may have read about Sanmay Ved, a researcher who was able to buy Google.com for one minute on Google Domains. Our initial financial reward to Sanmay - USD 6,006.13 - spelled-out Google, numerically (squint a little and you'll see it!). We then doubled this amount when Sanmay donated his reward to charity," Google said in a blog post.
Ved, in a post on LinkedIn, had said he chose his award to be donated to the Art of Living's education programme which runs 404 free schools across 18 states in India, providing free education to more than 39,200 children living in slums, tribal and rural belts where child labour and poverty are widespread.
Google said researchers from all over the world, coming from countries like Great Britain, Poland, Germany, Romania, Israel, Brazil, the US, China, Russia and India, participated in its security rewards programme.
"Tomasz Bojarski found 70 bugs on Google in 2015, and was our most prolific researcher of the year. He found a bug in our vulnerability submission form," the blog posted by Eduardo Vela Nava from Google Security team, said.
In 2015, the company gave $2 million in rewards to over 300 people. The programme which was started in 2010 has seen Google giving out over $6 million in rewards so far.
It said it has paid more than $200,000 to researchers for their work under Google's Android (mobile operating system) VRP programme launched in June.
This includes the largest single payment of $37,500 made to an Android security researcher.
"We also injected some new energy into these existing research programs and grants. In December, we announced that we'd be dedicating one million dollars specifically for security research related to Google Drive," the blog said.





Comments
Add new comment