Houston, Apr 17: Scientists, including one of Indian origin, have developed a unique camera that can capture detailed images of distant objects without using a long lens, an advance that could lead to telescopes that are less bulky. The system known as SAVI – for “Synthetic Apertures for long-range, subdiffraction-limited Visible Imaging” – does not need a long lens to take a picture of a faraway object, researchers said.The prototype built by researchers reads a spot illuminated by a laser and captures the “speckle” pattern with a camera sensor.
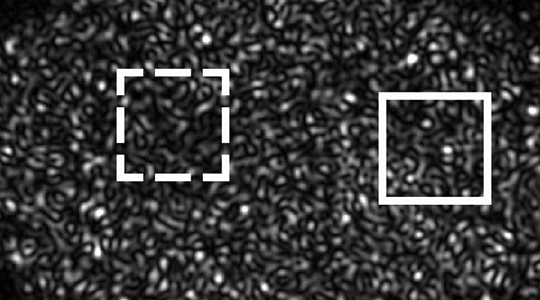
The prototype built by researchers reads a spot illuminated by a laser and captures the “speckle” pattern with a camera sensor.
Raw data from dozens of camera positions is fed to a computer programme that interprets it and constructs a high-resolution image.Researchers including those from Rice University in the US, built and tested the device that compares interference pat terns between multiple speckled images. Like the technique used to achieve the “Matrix” special effect, the images are taken from slightly different angles, but with one camera that is moved between shots instead of many fired in sequence. The prototype only works with coherent illumination sources such as lasers.
However, it is a step toward a SAVI camera array for use in visible light, researchers said. The speckles serve as reference beams and essentially replace one of the two beams used to create holograms, researchers said. When a laser illuminates a rough surface, the viewer sees grain-like speckles in the dot, as some of the returning light scattered from points on the surface has to go farther and throws the collective wave out of phase. The texture of a piece of paper – or even a fingerprint -is enough to cause the effect.
“Today, the technology can be applied only to coherent (laser) light,” said Ashok Veeraraghavan of Rice University.”That means you cannot apply these techniques to take pictures outdoors and improve resolution for sunlit images -as yet,” Veeraraghavan said.”With a traditional camera, the larger the physical size of the aperture, the better the resolution,” he said.
“If you want an aperture that is half a foot, you may need 30 glass surfaces to remove aberrations and create a focused spot.
This makes your lens very big and bulky,” he added. SAVI"s “synthetic aperture” sidesteps the problem by replacing a long lens with a computer programme the resolves the speckle data into an image, researchers said.
“You can capture interference patterns from a fair distance,” Veeraraghavan said. The research was published in the journal Science Advances.





Comments
Add new comment