Washington, Jul 9: Scientists, including those of Indian origin, have invented the first battery-less cell phone that consumes almost zero power and runs by harvesting energy from ambient radio signals or light.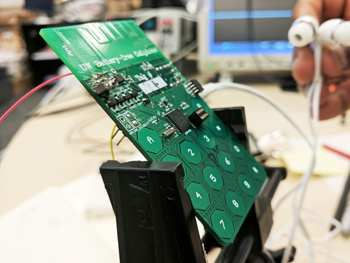
The team also made Skype calls using its battery-free phone, demonstrating that the prototype made of commercial, off-the-shelf components can receive and transmit speech and communicate with a base station.
"We have built what we believe is the first functioning cell phone that consumes almost zero power," said Shyam Gollakota, associate professor at the University of Washington (UW) in the US.
Researchers eliminated a power-hungry step in most modern cellular transmissions - converting analogue signals that convey sound into digital data that a phone can understand.
This process consumes so much energy that it has been impossible to design a phone that can rely on ambient power sources, researchers said.
Instead, the battery-free cell phone takes advantage of tiny vibrations in a phone's microphone or speaker that occur when a person is talking into a phone or listening to a call.
To transmit speech, the phone uses vibrations from the device's microphone to encode speech patterns in the reflected signals. To receive speech, it converts encoded radio signals into sound vibrations that are picked up by the phone's speaker.
In the prototype device, the user presses a button to switch between these two 'transmitting' and 'listening' modes, researchers said.
The prototype was able to perform basic phone functions - transmitting speech and data and receiving user input via buttons.
Using Skype, researchers were able to receive incoming calls, dial out and place callers on hold with the battery- free phone.
The team designed a custom base station to transmit and receive the radio signals. That technology conceivably could be integrated into standard cellular network infrastructure or Wi-Fi routers now commonly used to make calls.
"You could imagine in the future that all cell towers or Wi-Fi routers could come with our base station technology embedded in it, and if every house has a Wi-Fi router in it, you could get battery-free cell phone coverage everywhere," said Vamsi Talla, a research associate at UW.
The battery-free phone does still require a small amount of energy to perform some operations. The prototype has a power budget of 3.5 micro-watts.
Researchers demonstrated how to harvest this small amount of energy from two different sources. The battery-free phone prototype can operate on power gathered from ambient radio signals transmitted by a base station up to 31 feet away.
Using power harvested from ambient light with a tiny solar cell - roughly the size of a grain of rice - the device was able to communicate with a base station that was 50 feet away, they said.
The study was published in the journal Proceedings of the Association for Computing Machinery on Interactive, Mobile, Wearable and Ubiquitous Technologies.





Comments
Add new comment